Police raided ecstasy labs, seized vans with secret compartments for smuggling drugs and found submachine guns hidden behind false walls.
In every case deals were being made on Encrochat - an encrypted messaging service that used customised phones. It’s been called “WhatsApp for gangsters”.
Users thought they were safe to talk about deals for drugs, guns and even hitmen for hire. Hundreds of arrests left suspects baffled.
They had no idea that officers from the UK's National Crime Agency had data, messages and even photos sent over the Encro network after the French police hacked a server.
The hack in 2020 led to the biggest organised crime case in British criminal history and the data is still being investigated three years on.
But the police haven't had it all their own way and are now facing claims that they did not play by the rules.
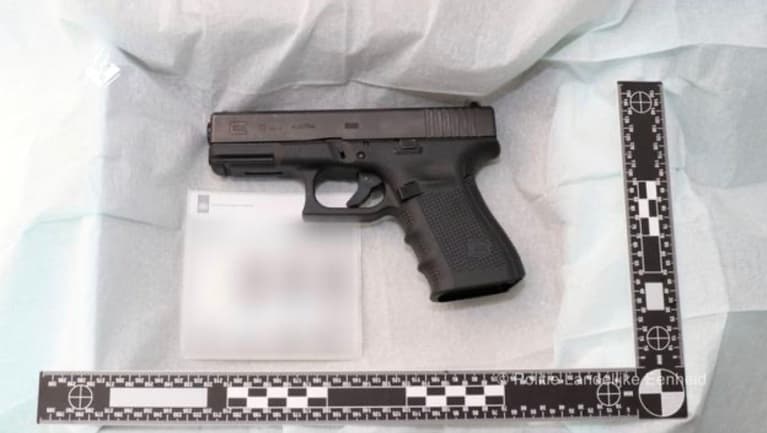
The investigation found groups buying and selling guns like these
"BIG BOSS"
The Encro investigation has led to the arrest of 3,000 suspects. Officers have seized nearly 10,000 kilos of cocaine and heroin, nearly 9,000 kilos of cannabis, 170 guns, 3,400 bullets and more than £75 million in cash.
Among the arrests was the award-winning rapper Nines, who admitted to importing 28 kilos of cannabis into the UK from Spain and Poland using the name “Big Boss” on the app.
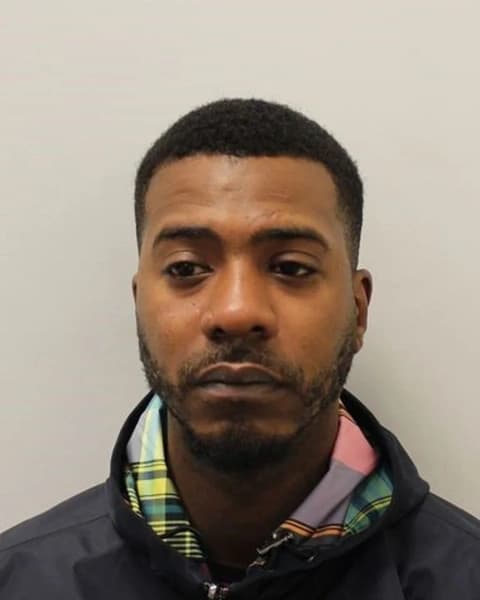
Nines, whose real name is Courtney Freckleton
Faye Dunn, a 38-year-old former women’s footballer who played for England at youth level, was jailed in September 2022 for her role as the accountant for her father’s drug smuggling gang.

Faye Dunn, ex women’s footballer who was jailed in September 2022
The early arrests and seizures mystified the suspects. After NCA officers raided an empty office block where an AK47 had been stashed, Bilal Khan, 33, messaged his accomplice: “Bro they found it. Makes zero sense but NCA have that AK.”
Khan, who called himself “Legend Killer” on the app, and gun dealer Umair Zaheer, who called himself “Assassin’s Creed” and hid Uzi and Skorpion submachine guns behind a false wall, were jailed in February 2022.
Five other men were also jailed after leaked messages uncovered a plot to murder a gangland rival.
The leaked data also uncovered the locations of massive labs making ecstasy across England, Wales and Scotland.
THE COURT CASES
Suspects across Europe who deny the charges against them are still awaiting trial. Many are questioning whether the French hack was legal and challenging the way that the NCA obtained the information.
So far the prosecutions in Britain have been almost entirely down to suspects admitting the crimes and pleading guilty.
A freedom of information request by TNM this month found that more than 90 per cent of all completed Encrochat cases relied on the suspect admitting the charges.
Of the cases that have so far been through court, only eight have ended with a jury finding the defendant was not guilty.
HOW DID THE HACK WORK?
The French police have never disclosed the full details of the hack, but it has become clear that it involved targeting the server, found in a town called Roubaix near the northern border with Belgium.
Court cases have heard that an “implant” put out a fake update for the Encrochat tech that allowed them to decode and view everything being said by thousands of users.
Roubaix, where police found the Encrochat server
DID THE POLICE PLAY BY THE RULES?
Across Europe there are now legal challenges to the way that the French officers carried out the hack and in the UK there have been a series of legal challenges to the way the NCA got hold of the data.
The latest challenge looks at the paperwork used to start the investigation.
Judges from the Investigatory Powers Tribunal - which decides whether police, spies and NCA agents are using their surveillance powers legally - are currently deciding whether the NCA used the correct warrant.
There are laws preventing the use of information from “live intercepts” - including recording phone calls - in court except in certain circumstances.
Lawyers for the suspects are arguing that the NCA applied for the wrong warrant and that none of the evidence from the chats should be allowed in court.
One claimed the NCA had misled judges and said one officer had been "wilfully blind" or "recklessly indifferent" to the information she was receiving before applying for the warrant.
A man is arrested as part of the investigation into Encrochat
The NCA’s lawyers told the court that the warrants were legitimate and said officers acted in good faith while working under intense pressure.
Accused of failing to consider laws protecting the privacy of “innocent users”, lawyers for the NCA told the tribunal that data linked to nearly 7,500 devices was examined by the NCA, but only 390 ( about 5 per cent) of the phones were not obviously being used by criminals.
The tribunal will rule in January 2023, with both sides expected to appeal if they lose. For the hundreds of suspects in prison, losing the case would mean continuing the long wait for a jury trial. For the NCA, losing the case would be a disaster, potentially leading to hundreds of criminal cases collapsing.
TNM will be covering the result and other developments as the Encrochat investigation continues.
You can see my explainer below on what Encrochat is all about. Follow on our socials @thenewsmovement for more.
TNM's Senior Reporter John Simpson reports on Encrochat